Have you ever wondered how your wearable devices capture data so quickly and accurately? The secret often lies in a technique called Double Direct Attack.
This method is changing the way wearables track your movements and health, making them smarter and more reliable. If you want to understand how this technology works and why it matters for your daily life, keep reading. By the end, you’ll see your wearable in a whole new light.
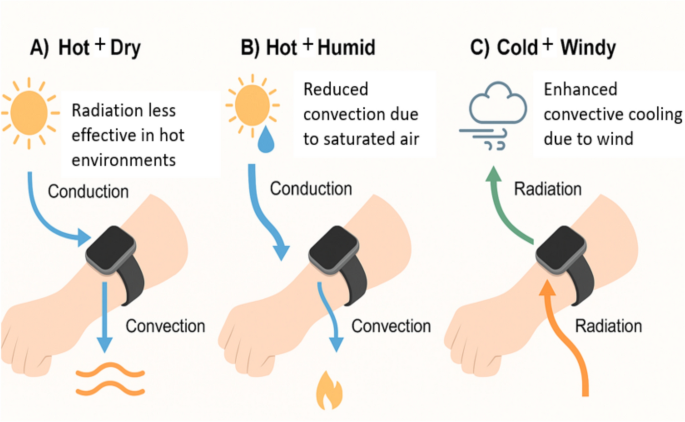
Credit: link.springer.com
Double Direct Attack Basics
Understanding the basics of Double Direct Attack in wearable technology is key to grasping how modern devices achieve higher accuracy and efficiency. This technique significantly improves the interaction between wearable sensors and the environment, providing better data collection and user experience. Let’s break down what this means and how it came to be.
Core Concept
Double Direct Attack involves using two separate but synchronized sensor inputs to capture data from different angles or sources simultaneously. This approach enhances precision by cross-verifying the signals in real-time, reducing errors commonly found in single-sensor setups.
Imagine you’re tracking your heart rate during a run. A single sensor might miss slight variations caused by movement or sweat. With Double Direct Attack, two sensors work together, compensating for each other’s weaknesses and delivering more reliable results.
This method not only improves accuracy but also speeds up data processing, allowing wearables to react faster to changes in your body or environment. You get real-time feedback that feels seamless and trustworthy.
Historical Development
The idea behind Double Direct Attack started gaining attention as wearable tech moved from simple fitness trackers to complex health monitors. Early devices often struggled with inconsistent readings, prompting engineers to experiment with multiple sensor inputs.
Over time, advances in microelectronics and signal processing made it possible to synchronize sensors efficiently without draining battery life. The adoption of this technique grew as users demanded more dependable performance from their wearables.
One breakthrough came from combining optical and electrical sensors, each attacking the data from a different angle—hence the term “Double Direct.” This hybrid approach paved the way for smarter, more adaptive devices that learn and adjust based on your unique physiology.
Have you noticed how your smartwatch seems to “know” when you start exercising, even before you tell it? That’s likely the Double Direct Attack at work, quietly improving your experience every step of the way.
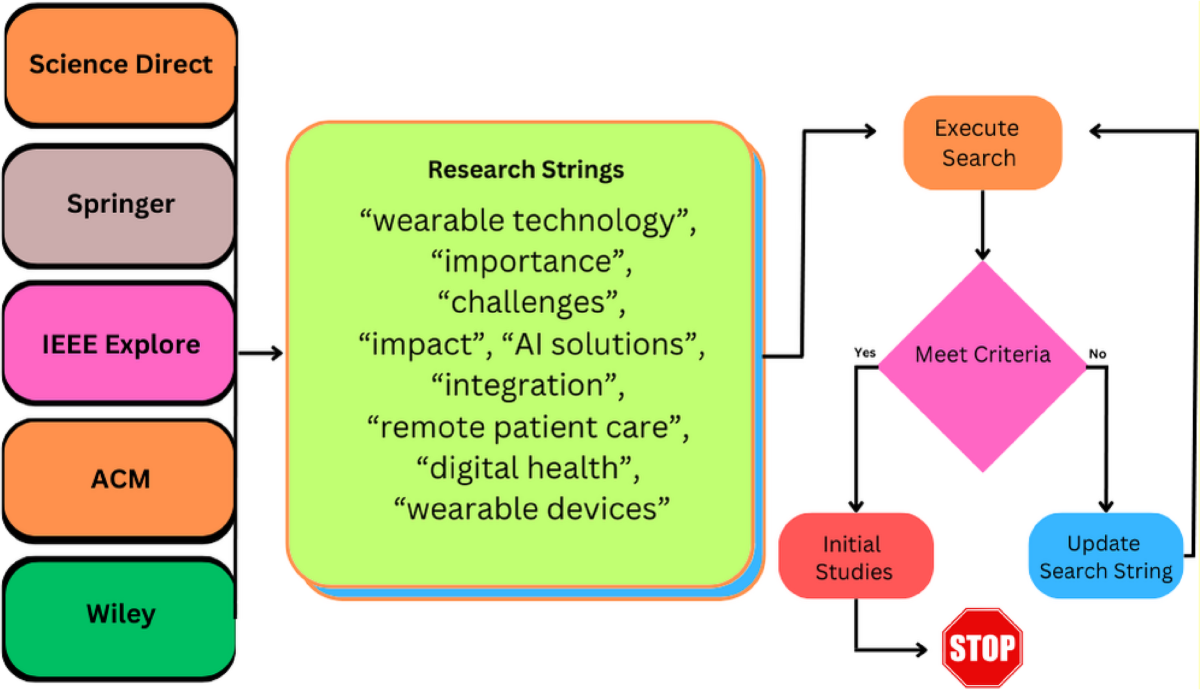
Credit: journalofcloudcomputing.springeropen.com
Technology Behind The Attack
The technology behind the Double Direct Attack in wearable technology involves precise hardware and software working together. This attack targets vulnerabilities in the device’s communication and data processing layers. Understanding the key components and how the attack operates helps reveal its impact on wearable devices.
Key Components
- Wireless Interface:Includes Bluetooth and Wi-Fi modules that connect the device to other systems.
- Sensor Array:Collects user data like heart rate, movement, and location.
- Processor Unit:Manages data processing and controls communication protocols.
- Firmware:Software embedded in the device that controls its functions.
- Security Modules:Encryption and authentication systems designed to protect data.
Operational Mechanism
The attack exploits weaknesses in the wireless interface and firmware. It sends simultaneous signals to confuse the processor unit. This confusion allows the attacker to bypass security modules.
Attackers intercept data from sensors while also injecting false data. This double approach creates errors in the device’s operation. The wearable device then sends inaccurate information to connected systems.
By targeting both data input and communication channels, the attack gains control over the device. It can steal sensitive information or disrupt normal functions without detection.
Applications In Wearable Devices
The Double Direct Attack technique enhances wearable devices by improving data accuracy and response times. This method allows wearables to process signals from two points simultaneously. It creates more reliable results. The technology is useful in several wearable applications. It helps devices to be smarter and faster.
Health Monitoring
Double Direct Attack improves health sensors in wearables. It helps measure vital signs like heart rate and blood pressure more accurately. The technology detects small changes quickly. This early detection can alert users about health issues sooner. It supports continuous monitoring without delays. Users can trust the data for better health decisions.
Fitness Tracking
Fitness devices use this method to track movements with precision. It captures data from different muscles or limbs at the same time. This gives a detailed picture of workouts and activity levels. Users get exact information on steps, calories, and exercise intensity. The technology ensures fitness plans are based on real performance.
Security Features
Wearables employ Double Direct Attack to enhance security functions. It strengthens biometric authentication like fingerprint or vein scanning. The method reduces errors and false readings. It makes it harder for unauthorized users to access devices. This adds a strong layer of protection for personal data.
Advantages Over Traditional Methods
Double Direct Attack offers clear advantages over traditional methods in wearable technology. It enhances data capture and analysis, leading to better performance. This approach reduces errors and saves time in various applications. Users gain more reliable results and smoother experiences.
Enhanced Accuracy
Double Direct Attack improves the precision of sensor readings. It captures data from multiple points simultaneously. This reduces the chance of missing important signals. Traditional methods often rely on single-point data collection, which can be less reliable. The technique helps deliver consistent and accurate feedback for users.
Improved Efficiency
This approach speeds up the data processing time. It minimizes the steps needed to analyze information. Devices using this method can work faster and with less power. Users benefit from quicker responses and longer battery life. Efficiency gains make wearable devices more practical for daily use.
Challenges And Limitations
Double Direct Attack in wearable technology faces many challenges and limits. These issues affect how well the technology works and how people accept it. Understanding these difficulties helps improve future designs and user trust.
Technical Barriers
Wearable devices must handle complex data quickly. Processing two direct attacks at once needs high computing power. Many wearables have limited battery life and small processors. This limits their ability to manage attacks efficiently.
Signal interference is another problem. Wearables rely on wireless connections that can be disrupted. Such disruptions can weaken the device’s defense against attacks. Also, hardware must be robust to avoid failures during attacks.
Privacy Concerns
Double Direct Attack involves sensitive user data. Protecting this data is critical to avoid misuse. Wearables collect personal health and location information. If attacked, this data can be stolen or exposed.
Users often worry about who controls their data. Lack of clear privacy policies reduces user trust. Ensuring strong encryption and transparent data use is essential. Without these, privacy risks remain high.
Future Directions
The future of Double Direct Attack in wearable technology holds exciting possibilities. This approach will drive new designs and smarter devices. Advances in materials and sensors will improve performance. Devices will become more efficient and user-friendly. The next steps focus on enhancing accuracy and battery life. Developers aim to create wearables that adapt better to user needs. These trends will shape how people interact with technology daily.
Innovations On The Horizon
- Integration of flexible electronics for better comfort
- Enhanced real-time data processing with AI
- Improved energy harvesting to extend device use
- Smaller, more powerful sensors for precise detection
- Advanced wireless communication for faster data transfer
Potential Industry Impact
Double Direct Attack will influence healthcare by enabling early diagnosis. Fitness trackers will offer more accurate health insights. The sports industry will benefit from detailed performance data. Consumer electronics will see smarter, more responsive wearables. These changes will create new jobs and business opportunities. Industries will adopt this technology to improve services and products.
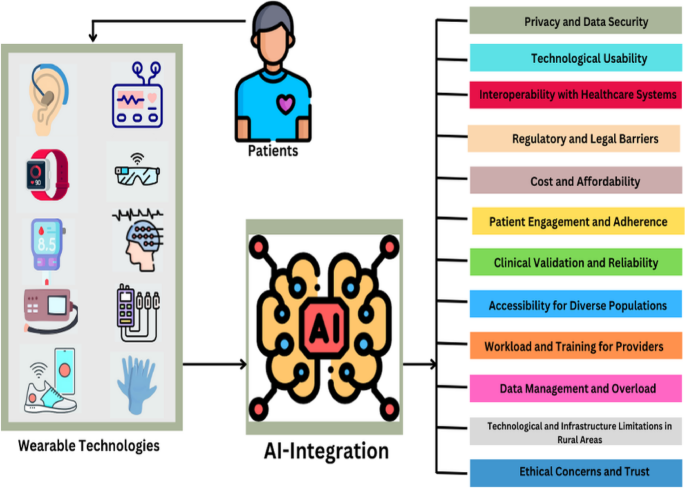
Credit: journalofcloudcomputing.springeropen.com
Frequently Asked Questions
What Is Double Direct Attack In Wearable Technology?
Double Direct Attack is a security method used in wearable devices. It involves two simultaneous attack vectors targeting hardware and software. This approach helps identify vulnerabilities and enhances device protection against cyber threats.
How Does Double Direct Attack Improve Device Security?
It detects weaknesses by combining hardware and software attack strategies. This dual approach exposes hidden flaws, allowing developers to strengthen defenses. It ensures comprehensive protection for wearable technologies.
Which Wearable Devices Use Double Direct Attack Techniques?
Smartwatches, fitness trackers, and medical wearables commonly implement this technique. These devices require robust security due to sensitive personal data. Double Direct Attack helps maintain data integrity and user privacy.
What Are The Risks Of Ignoring Double Direct Attack Methods?
Ignoring these methods leaves devices vulnerable to hacking and data theft. Cybercriminals can exploit single-layer defenses easily. Utilizing Double Direct Attack reduces security breaches and protects user information.
Conclusion
Double Direct Attack poses a real threat to wearable tech. Understanding these risks is crucial for users. It helps in safeguarding personal information. Consider using strong passwords and updated software. Awareness of potential vulnerabilities is key. Regular checks can prevent unwanted breaches.
Always stay informed about security updates. This way, you keep your devices safe. Remember, protection starts with knowledge. Wearable technology continues to evolve. So should your approach to security. Stay alert and proactive. Your data and privacy depend on it.
Leave a Reply